Decentralized finance (DeFi) is widely regarded as a groundbreaking advancement in finance, as frequently asserted by numerous cryptocurrency enthusiasts. The creation of a novel space has the potential to provide users with fresh opportunities to generate income while simultaneously contributing to a community-driven initiative of significant magnitude. However, it should be noted that DeFi’s advancements are accompanied by certain drawbacks. The cryptocurrency industry is replete with fraudulent activities, including scams related to Bitcoin (BTC), blockchain, and other wallet-endangering situations.
The DeFi sector experienced $12 billion in cryptocurrency scams and theft in 2021, resulting in the loss of crypto assets from user wallets and exchange holdings. A portion of the theft can be attributed to inadequately designed smart contracts and vulnerabilities in platform security. In contrast, the remaining amount can be attributed to cryptocurrency fraud, wherein malicious agents exploited inexperienced users in the field. For the cryptocurrency industry to achieve widespread adoption, fraudulent activities and vulnerabilities in security must be effectively addressed.
Regrettably, it is likely to take a considerable amount of time for the industry to effectively address the problem of fraudulent activities related to blockchain technology. Until it arrives, the present guide aims to instruct users on the mechanics of cryptocurrency scams and how to identify them. This article aims to guide identifying and mitigating the risks associated with cryptocurrency and decentralized finance (DeFi) scams. Although it is unfeasible to completely eradicate cryptocurrency fraud and theft within the industry, DeFi traders must remain vigilant of the following prevalent scams.
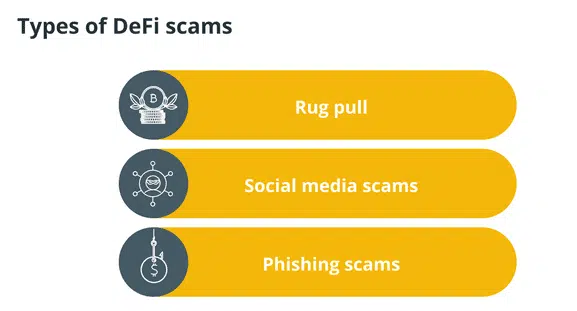
A Rug Pull
Rug pulls are widely considered to be among the most prevalent forms of cryptocurrency scams within the DeFi domain. However, they can be relatively straightforward to detect for individuals who possess the requisite knowledge and expertise. A rug pull refers to the promotion of a seemingly innovative project by developers. They amass many supporters and secure substantial financial backing from investors, potentially reaching the millions. Subsequently, the developers vend the tokens and abscond with the funds. The developers did not intend to utilize the investors’ funds to construct a project. They planned to engage in fraudulent activity. In the event of a sudden depletion of investor funds, the project would be defunct. Investors experience a sudden and significant loss of investment value.
By closely examining a developer’s engagement with their communities and their strategies for distributing tokens, it is possible to identify instances of rug pulling readily. If a project neglects to specify a token lock-up period, particularly regarding the developers, the team members are granted unrestricted access to the tokens at any given time. Collaborating with projects that implement extended token lock-up periods is advisable as a safeguard against the potential misappropriation of funds by developers. Typically, these initiatives will exhibit high transparency with their stakeholders, furnishing regular progress reports and a comprehensive roadmap. Although not limited to DeFi, a pump and dump scheme resembles a rug pull.
Social Media Scams
Scam accounts that impersonate celebrities, including those in the cryptocurrency industry and non-crypto-related individuals, are prevalent on the Twitter platform. Notwithstanding, these impostors will contact individuals who are enthusiastic about cryptocurrency about their novel undertaking and may feign possession of giveaways and contests, requiring users to transfer funds to a designated address. Verifying the authenticity of these accounts can be accomplished with ease. An individual who assumes the identity of a celebrity is likely to possess a relatively modest number of followers, in contrast to the substantial following of the authentic celebrity account, which may number in the millions. Frequently, these accounts exhibit rudimentary grammatical inaccuracies and orthographic mistakes. In any case, avoiding engaging in any financial transaction with a Twitter account is advisable.
Phishing Scams
Phishing emails may contain hyperlinks to fake websites resembling legitimate platforms, luring unsuspecting individuals to disclose their confidential data, which is then secretly acquired by the perpetrators. To mitigate the risk of falling prey to fraudulent blockchain schemes, it is imperative to consistently verify the legitimacy of the contact’s email address. The electronic mail message may frequently contain arbitrary symbols instead of a legitimate web address. It is advisable to refrain from clicking on any hyperlink that appears dubious in an email. To mitigate potential security risks, it is advisable to manually access a platform’s website and verify URLs to prevent falling prey to fraudulent activities. One example of ensuring website security is verifying the presence of an HTTPS security certificate and ensuring the accuracy of the URL spelling.
Additional Security Measures
It is imperative to remain vigilant for the aforementioned fraudulent activities within Decentralized Finance (DeFi). However, certain generalized approaches can aid in avoiding inclusion on a list of victims of cryptocurrency scams.
Two-Factor Authentication (2FA)
Regardless of the DeFi domain an investor chooses to allocate their resources, all platforms should incorporate a variant of two-factor authentication. Two-factor authentication (2FA) is a security measure that involves the transmission of a text message or email to a previously authenticated account, which is mandated after the provision of a password. In this manner, if an unauthorized individual obtains one’s password, additional mobile device or email access would be required to successfully breach an account.
Use a Hardware Wallet
Hardware wallets are physical devices that enable users to securely store their private keys externally. With the progression of the DeFi sector, an increasing number of decentralized applications (DApps) are now capable of integrating with hardware wallets. This allows users to securely store their assets while conveniently accessing their preferred DeFi platforms. Despite the provision of such a wallet by a platform, suggesting the storage of assets in an online wallet poses a challenge. The act of storing assets online exposes users to the risk of theft. Decentralized Finance (DeFi) breaches frequently culminate in the loss of substantial amounts of funds, impacting numerous users. By revoking a platform’s authorization to access users’ funds, individuals enhance their security measures by one degree.
Investigate a Community
DeFi projects that achieve success frequently foster a productive community comprising engaged users and developers in reciprocal communication. Effective communication is crucial for the secure development of a platform that all can enjoy.
It is worth noting that in the case of a project with developers who are inactive or uncommunicative, there exists a possibility that they may be devising a fraudulent scheme such as a rug pull. According to crypto enthusiasts, knowing the team responsible for a particular project is advisable. If a team opts to withhold their plans or abstain from communicating with their community, it may be inferred that their intentions are unfavorable.
It is widely acknowledged as optimal to engage in undertakings that possess flourishing communities and, in addition, conduct supplementary investigations before establishing a viewpoint. It is also possible to consider the inclusion or exclusion of a token in listing platforms and the reasons behind such decisions. If a listing platform denies a token, it is advisable to refrain from investing in it.


